AdwareSpywareDetective is designed to be simple and easy
to use. It's design facilitates the quick action necessary to rid
your PC of Spyware & Adware Parasites. The AdwareSpywareDetective
Interface consists of 6 control buttons:
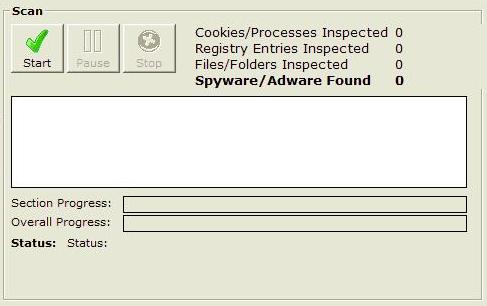
Scan Now
| Clicking the Scan Now starts the scanning process for spyware,
adware and other threats.When this button is clicked the following
screen will appear: |
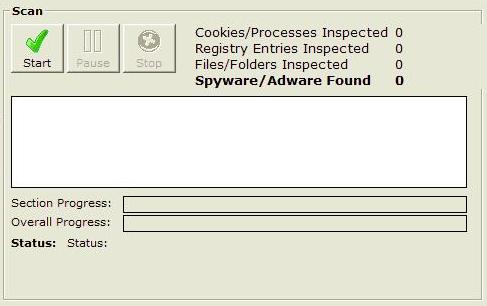 |
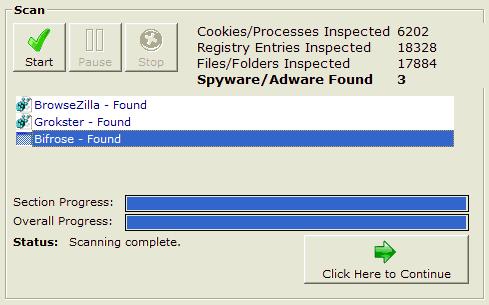
| Once the "Start" button is pressed the scan will
begin. As each area of your PC is scanned any threats detected
will begin to appear in the scan status window. The scan should
take no longer than 1 minute. When the scan is complete the
"Click Here to Continue" button will appear. You can
stop the scan at any time by pressing the "Stop" button
or pause the scan by pressing the "Pause" button. |
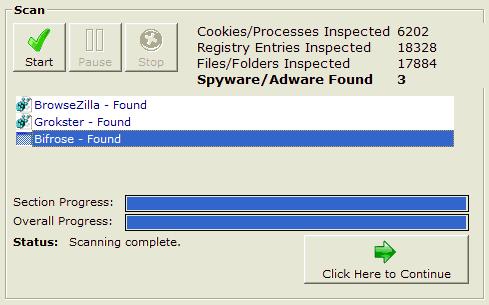 |
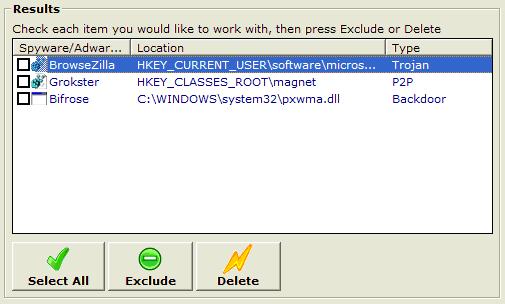
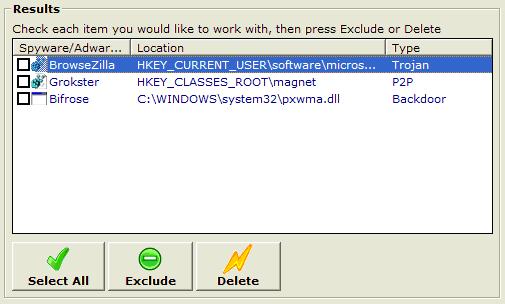
| Once the scan is finished a list of detected threats found
on your computer will be visible. Press the "Click Here
to Continue" button. From here you can decide what threats
you would liked removed from your system. Any threats that are
deleted will be backed up to the Quarantine folder in the directory
that you installed this program in. |
 |
Settings
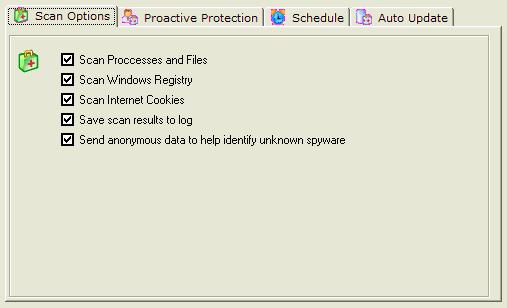
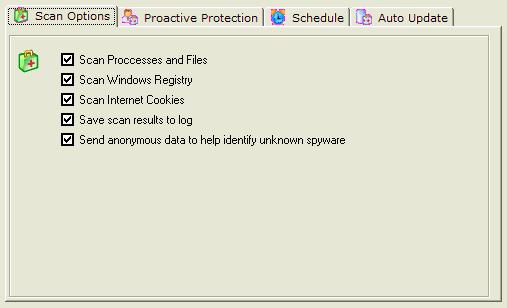
AdwareSpywareDetective has 4 main setting tabs. the first
is tab is "Scan Options". We recommend that all 5
options are selected as it allows a comprehensive search for
threats Scan Processes and Files
Running processes are
programs that are open on your computer. If adware or spyware
is currently running on your computer it will be detected by
scanning running processes.
Scan Windows Registry
Many spyware and adware programs place entries into your system
registry that allow them to be executed when you turn on your
computer, or track information about you. If these registry
entries are present on your computer they will be detected.
Scan Internet Cookies Many websites track personal
information using cookies. Most cookies are harmless, but some
are used to track your browsing habits and target you with advertising,
or store personal information without your consent. If these
cookies are present on your computer they will be deleted.
Save Scan Results to Log This option will allow
you to view a log of your scans using the View Log button.
Send Anonymous Data
A feature of AdwareSpywareDetective is to detect threats that
are not included in the 42,000 threat definition database. If
an unknown threat is detected it can send details of this threat
to be included in the next threat definition update. |
 |
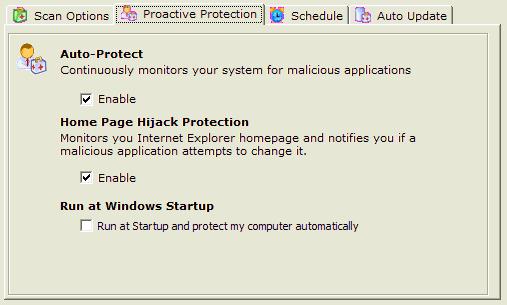
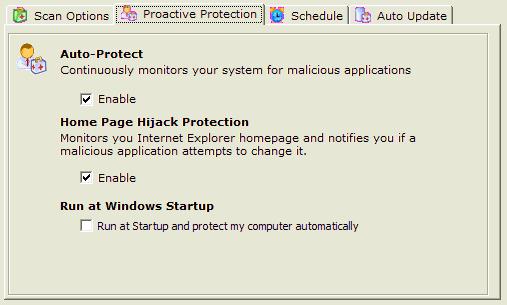
The second tab in settings is "Proactive protection"
Auto-Protect Auto-Protect
To ensure your PC is safe at all times AdwareSpywareDetective
continuously monitors your system's memory in search of threats.
Some threats can cause harm to your computer just seconds after
running, so enabling Auto-Protect is an important step to stopping
those threats dead in their tracks. If a threat is detected
you will be alerted automatically, and you will be given the
option to stop the threat from running. We recommend performing
a system scan immediately afterwards to remove any files or
registry entries that the threat may have created. Home
Page Hijack Protection
Many spyware and adware programs will attempt to change your
Internet Explorer Home Page and direct you to another site.
Their motivation might be to get you to download new adware/spyware,
display ads to bring in revenue, or direct you to a web page
that pays them for web traffic. Enabling Home Page Hijack Protection
will allow us to alert you whenever your homepage changes, and
allow you to choose whether or not to allow that change to be
made. Run at Windows Startup
Enabling this
option will allow this program to run automatically whenever
you turn on your computer. We recommend leaving this option
checked all the time. |
 |
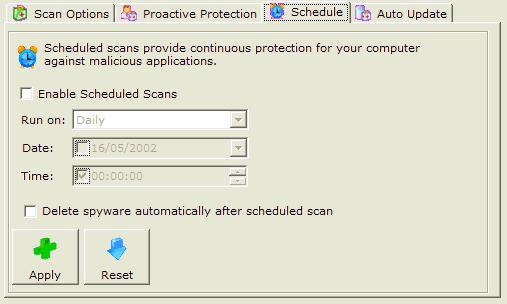
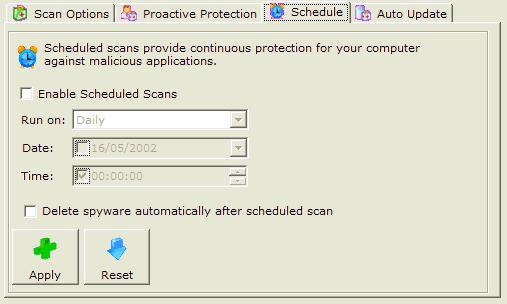
| The third tab in settings is "Schedule".The schedule
allows AdwareSpywareDetective users to scan their PC at a specific
time or date. |
 |
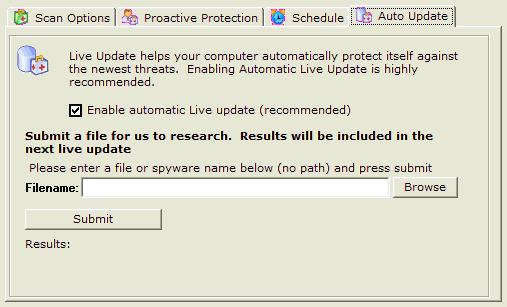
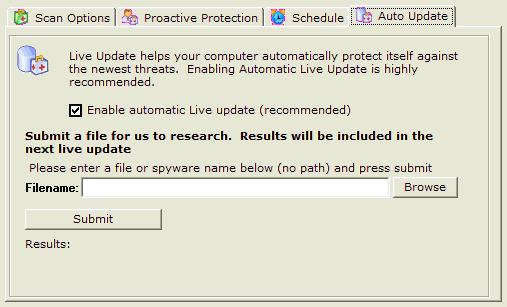
The final tab in settings is "Auto Update". Enabling
Auto Update allows your computer to periodically run Live Update
and ensure that you always have the most recent definition files
available. Definition files are updated as new threats emerge,
and we recommend that you leave this option checked all the
time.
|
 |
View Log
| You can view your most recent scan log by clicking the View Log button.
After each scan a log is created that serves as a record of
the scan's activity. It provides you with details of the scan,
how many items were scanned, and the locations that threats
were located. |
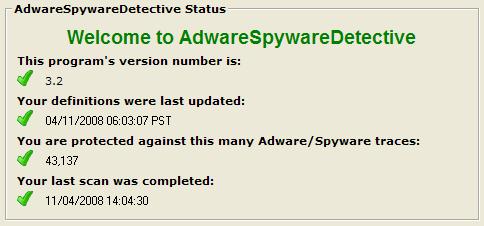
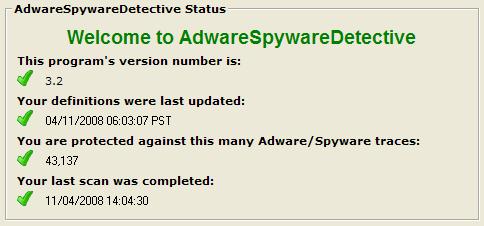
Status
| The status area displays information about this program, including the version number, definition file number, the number of Adware/Spyware applications it protects you against, the number you have removed, and the date your last scan was completed.
|
 |
Live Update
| Clicking the live update button will automatically connect to our server to check for the newest threat definition files. We periodically update these definition files as new threats emerge. You can also enable Auto Update in the settings area so that the program will automatically check for updates.
|
Send To Tray
| Moves AdwareSpywareDetective to your toolbar on your desktop |
|